P2P | What is P2P (Peer-to-Peer) Definition
This is a comprehensive guide based on P2P or Peer To Peer with a complete explanation.
What is P2P?
In peer-reviewed (P2P) media, a set of servers have been linked with equivalent permissions and duties for processing info. Unlike conventional social media, zero apparatus in a P2P system is given exclusively to function or even get info.
Humans were genuinely have been thought to produce a peer system network of nodes. Peers create a part of these tools, like computing capacity, disc or system bandwidth, even directly readily available to additional network participants, even with no demand for fundamental manipulation with servers or servers that are stable.
Humans are suppliers and users of all funds, compared to the usual Client-server product where the ingestion and distribution of funds have been broken.
Rising collaborative P2P devices are moving past the age of friends accomplishing comparable matters while discussing tools.
They want assorted peers who may bring about exceptional tools and skills into some digital network, enabling it to activate in tasks that are greater beyond the ones which will be done by different peers, even favourable to most of those tech peers.
Even though P2P devices are utilized in many applications domain names, the structure was popularized with the document-sharing platform Napster, first published in 1999.
The theory has motivated new constructions and characteristics in most regions of individual interaction.
In such societal contexts,” peer-reviewed being a me-me denotes the egalitarian social networking that’s emerged across modern culture, empowered by Web technology generally.
P2P File Sharing
When you find several valid applications for P2P media, the document sharing facet increases equally intellectual real estate along with cyber-security worries.
Whenever folks discuss audio, pictures, applications, or every other personal material, inquiries of intellectual property and copyright legislation, the truth is that some online providers have experimented with prohibiting torrents along with different P2P programs.
It even despite the legitimate and legal purposes P2P could function. Anytime you are mindful of P2P media, you have possibly found out of any of this at the Feeling of document sharing.
For example, P2P application such as Kazaa and Napster has been a standard detection over the average household consumer’s pc. These apps let customers exchange huge files on the Web, on average movies and music.
As opposed to using virtual servers because of this intention, they utilized their own global userbase’s computer systems as each customer and host (i.e. P2P), effortlessly offloading processing heaps on your users.
Even though these apps are now not in drama, P2P filesharing is still living and very well (assume Bit Torrent and such). Even instant message (IM) customers will function this particular function, as the vast bulk of these encourage sharing data documents and conversing.
Development of P2P
Even though P2P devices are utilized in many application domains, the concept had been popularized by document sharing techniques like the music-sharing app Napster (formerly published in 1999).
The peer-reviewed movement enabled tens of thousands of internet surfers to join”specifically, forming classes and cooperating to eventually turn into user-created hunt motors, digital supercomputers, and file-systems.”
The simple idea of peer-reviewed computing has been pictured from previous applications approaches and media talks, attaining straight back once again to fundamentals mentioned within the very first Ask for Remarks, RFC.
For that reason, USENET, a distributed messaging method which is frequently described being an early peer-reviewed structure has been created. It had been designed in 1979 being something which occupies a de-centralized product of controller.
The basic version is just a ClientServer version by the client or user outlook that provides a more Self Organizing way of News Group servers. But, information programs keep in touch with the other person as friends to disperse Usenet information content posts within the whole set of servers.
Precisely the Exact Same thing applies to SMTP email from the Feeling which the centre email-relaying community of email transport brokers comes with a peer character persona.
In contrast, the periphery of both email customers and their immediate relations is a mutual connection.
Tim Berners-Lee’s eyesight to its Internet was near your P2P system as it supposed just about every consumer of this Web would be a lively contributor and editor. Also, linking and creating articles to sort an interlinked “worldwide internet” of back inbound backlinks.
The ancient Web was open compared to every afternoon, by which two servers joined to the NNetcan send out packets to each other devoid of firewalls and other safety actions.
It contrasts with the broadcasting-such as the arrangement of this nNetas it’s evolved through many recent ages. for a precursor into the Web, ARPANET proved to be a prosperous social media at which”just about every single engaging node will ask and function articles.
” But, ARPANET wasn’t self-organized, plus it could not “give any way of circumstance or content-based routing over and above uncomplicated’ address-based routing.”
Architecture of P2P
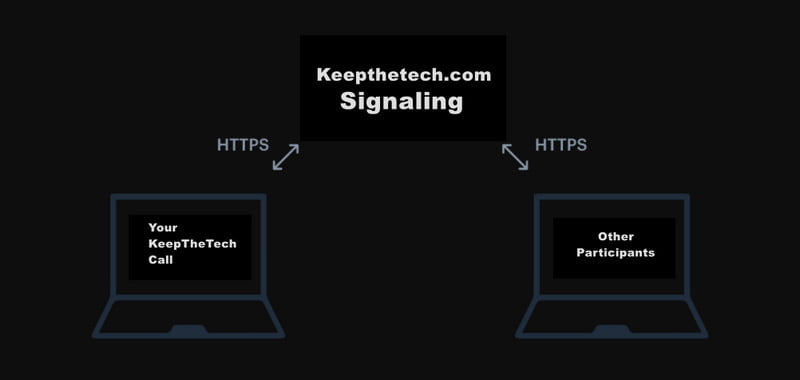
A peer system network was made around the concept of the same peer-reviewed nodes concurrently working as both”clients” and”servers” for one different node in your system. This version of network arrangement is different from your consumer –server version in which communication is often to and out of a centralized server.
A more standard instance of a document transport that employs the ClientServer version could be your File Transfer Protocol (FTP) assistance. Your server and client apps are somewhat different: the customers commence the move, and the servers meet those orders.
Structured P2P Networks
Even the most frequently encountered kind of structured P2P systems employ a dispersed hash table (DHT). A version of persistent hashing can be utilized to assign possession of every single document to some peer.
It empowers engineers to look for tools on your system using a ribbon dining table: this is, (crucial, worth ) pairs have been kept at the DHT, and also some engaging node can effectively regain the price related to any essential.
Back in ordered peer-to-peer networks, the overlay is coordinated to some particular topology. The protocol also implies any node can economically hunt the system to get a file/resource, even whenever reference is exceptionally infrequent.
Unstructured P2P Networks
Unstructured peer-to-peer systems tend not to enforce a specific arrangement on the overlay system by designing but are shaped with nodes that intentionally sort links to one another. (Gnutella, Gossip, along with Kazaa, are cases of coordinating P2P protocols).
While there isn’t any structure internationally levied upon these, unstructured networks are simple to develop and invite localized optimizations to distinct elements of this overlay.
Additionally, as the function of most peers within the system is precisely the exact very same, unstructured networks are potent on the surface of elevated levels of”churn”–which is, even when substantial quantities of friends are generally linking and departing the system.
Wrapping Up
Here we got the knowledge and insights on P2P which stands for Peer-to-Peer network. We discussed its basic structure and its development of it. Give a read here.
FAQ: Frequently Asked Questions
These are some of the frequently Asked Questions related to the P2P with complete information.
What is P2P and how does it work?
A collection of computers is joined together with equal permissions and responsibilities for data processing in peer-to-peer (P2P) networking. In contrast to traditional client-server networking, no device in a P2P network is completely dedicated to serving or receiving data.
What are P2P devices?
A P2P (peer to peer) connection is a direct link between two peers: a client device (such as a smartphone or laptop) and an IoT device (such as a surveillance camera, smart door lock, alarm system, heat controller, or anything else that can connect to the internet)
What is P2P Procure payment?
Procure-to-pay, also known as P2P or purchase-to-pay, is the process of requisitioning, acquiring, receiving, paying for, and accounting for goods and services, encompassing the complete process from point of order to payment.
Is P2P a DNS?
The Domain Name System (DNS) is an important Internet service. DNS is largely used to translate human-memorable names to IP addresses, which are used for routing but are generally meaningless to humans. The hierarchical nature of DNS, on the other hand, makes it inappropriate for a variety of Peer-to-Peer (P2P) Name Systems.
Related Articles:
Ultimate Guide To Setup Arch Linux
How to Make a Youtube Banner – Ultimate Guide
How To Cancel Google Stadia Subscription
My Apron Login – Home Depot ESS Home Depot Schedule
How To Make A Magical Express Reservation Online
20 Pet Tracking Apps For iPhone / Android
3 Ways To Remove Contact Support In Windows 10
25 Best YouTube Channels To Learn Cooking
15 Ways To Customize Laptop Like A Custom Laptops
How To Change Color of Start Menu In Windows 10
How To Import All Bookmarks From Chrome To Firefox