10 Advanced IP Scanner and Tracker
Are you looking for an advanced IP Scanner or IP tracker? Then don’t worry here we have listed some of the best and most advanced IP trackers.
These web tools allow you to scan the network and find the loop in your network connection.
What are IP Scanners?
Internet protocol scanners discover many different loopholes of the system and protect against abnormal and unprecedented behaviour that poses a menace to the machine.
Also, it supplies a handy means to affix your laptop or pc network. It is just a handpicked set of Best internet protocol address Scanners, having its favourite capabilities and blog links.
The checklist comprises the available source(of no cost ) and industrial (compensated ) system scanning applications.
Indeed, one of those hard actions for community directors would always be to take care of the IP address handle. It will become complex whenever you work in a vast organization within which tens of thousands of programs connect.
Managing IP addresses from the dictionary isn’t elaborate. It becomes cluttered whenever you have 1000s of IPs.
Here we have listed a few IP scanners available online:-
1. Angry IP Scanner
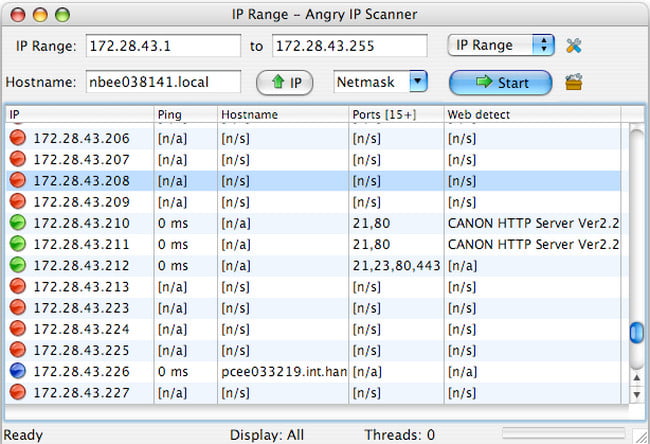
It’s an open-source and free system scanning utility having the skill to scan IP addresses and performs interface scans economically and economically.
Its checking record includes information like hostname, NetBIOS (Network essential Input/Output technique ), MAC address, computer name, workgroup info, etc.. ) Report creation is currently in CSV, Txt, or XML structure.
It’s dependent upon the Multi-threaded Scanning tactic that’s another scan ribbon for every person’s IP speech and helps improve the scanning procedure.
2. Snort
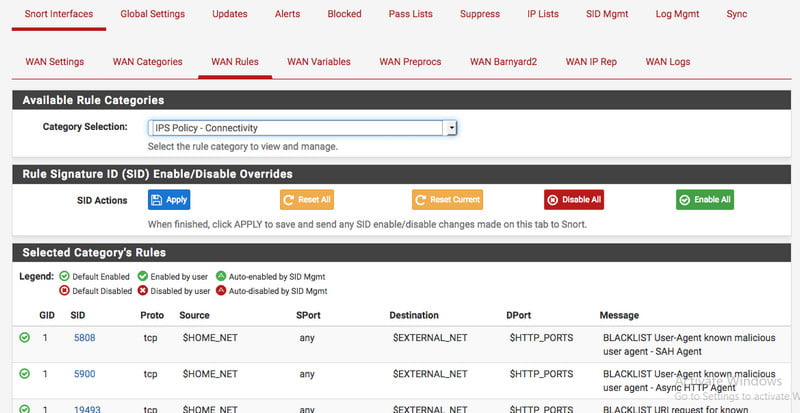
Snort is popularly called an entirely complimentary and accessible system intrusion detection and avoidance approach.
It assesses community traffic together with internet protocol dealing with passing. Snort can discover pig, interface scan, and also other systems harness protocol analysis and information hunting.
Snort Employs a Modular Detection Motor and Both Side Safety Engine(BASE) to characterize community traffic.
3. Nessus
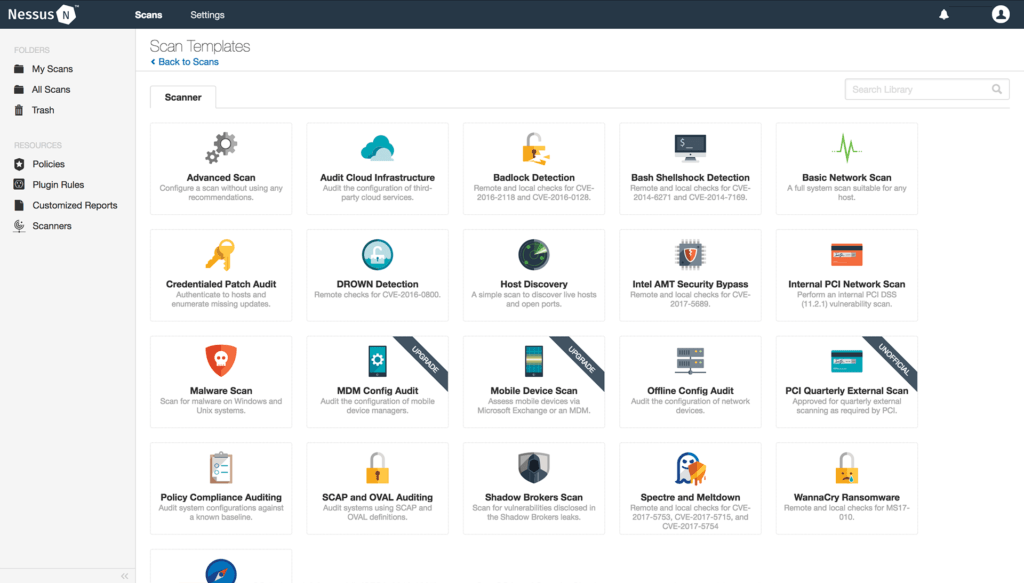
It’s a popular social system security scanner which is employed together with all the UNIX techniques. The application has been free and open-source.
However, today, it’s obtainable as a mobile application. The most entirely free model of Nessus comes with confined security attributes.
Nessus now comes with 70,000+ plugins and services/functionalities like malware detection, web program scan, platform setup test, etc.
The progress attribute of Nessus is automatic scanning, multi-network scanning, and strength discovery. Nessus can obtain three variants like Nessus Household, Nessus Skilled, and Nessus Manager/Nessus Cloud.
4. Advanced IP Scanner
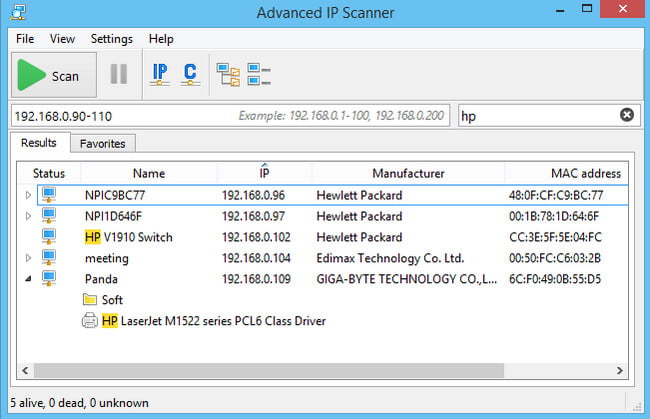
Being free and in the open-source form of the scanner, it efficiently works in the Windows environment. It can perform the detection of the network, which also includes wireless devices.
This IP Scanner allows the services through FDP, RDP, and HTTP on the remote machine’s device. It also performs the accessing of remote, easy shut down of the system, and LAN service.
5. SolarWinds
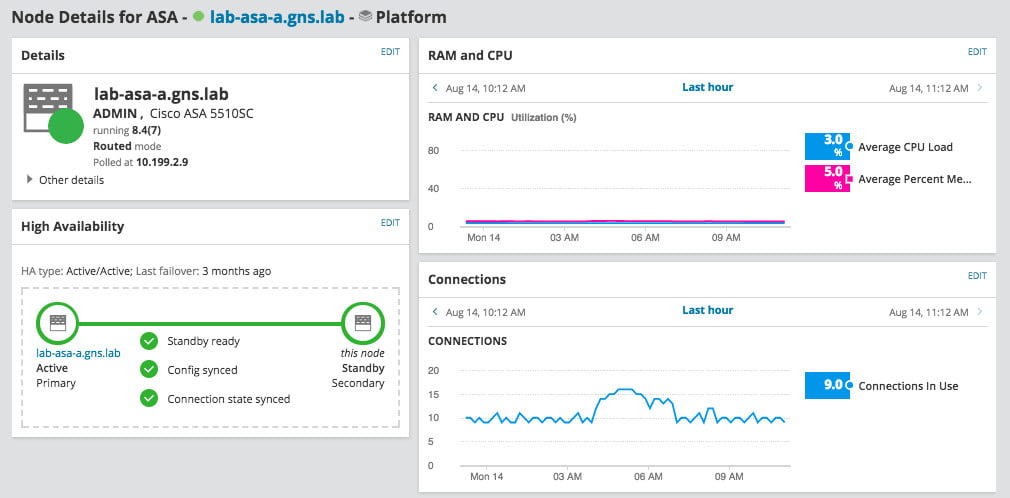
SolarWinds provides the Network Unit Scanner with Network Performance Monitor to monitor, Find a map, and scan the System Apparatus. Such Network Discovery software will run as soon as or planned for routine discoveries to pinpoint newly added apparatus.
An entirely operational trial offer will design for 30 days. Network functionality observe value begins at $299. This network system Scanner will immediately detect and scan the system apparatus. You will have the ability to map system topology.
It’ll provide error, accessibility, and effectiveness instructions for your appliance onto this system.
This Network Performance Monitor offers a customizable dash to produce such details. It will supply the primary source faster during smart, dependency & topology-aware network alarms. It will perform a hop-by-hop investigation of cloud and on-premises software & solutions.
6. Intruder Network Scanner
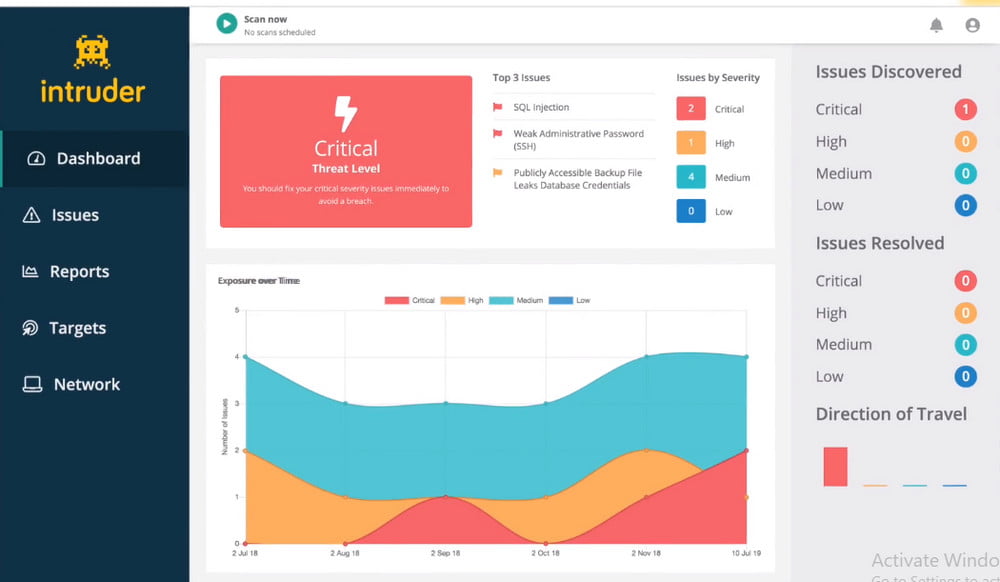
With tens and 1000s of automatic safety checks readily available, Intruder creates enterprise-grade vulnerability scanning obtainable for organizations of all measurements.
Its protection checks include pinpointing misconfigurations, overlooking stains, and ordinary web application problems like SQL shot & cross-site scripting.
Constructed by seasoned security pros, Intruder protects a lot of the bother of vulnerability direction, so you may concentrate on that which matters.
It saves time by assigning results predicated on their circumstance to proactively scans your processes for your most recent vulnerabilities; therefore, you never should worry about that.
An intruder can be just really an effective vulnerability scanner that locates cyber-security flaws on your system platforms.
It also explains why the risks and helps by using their remediation in front of a breach may happen you can also use the pen testing services for the proper solution. Intruder additionally incorporates cloud services in addition to Slack & Jira.
7. WireShark
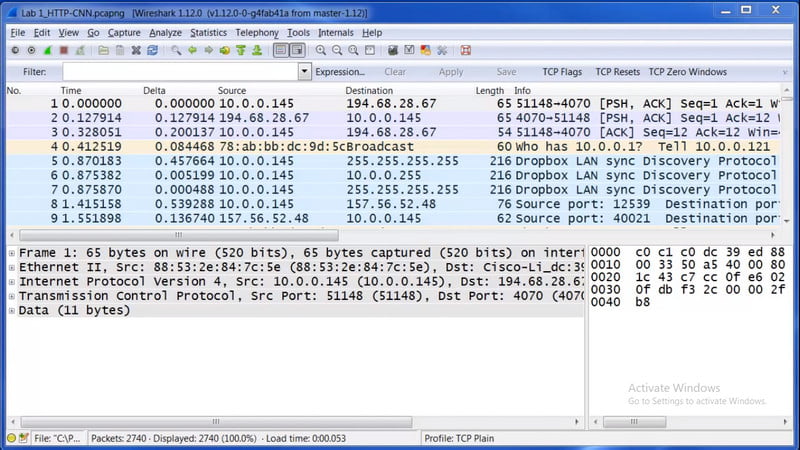
Wireshark can be an open-source application tool that’s called a more multi-platform system protocol analyzer.
It arranges info vulnerabilities to stay networking between your busy server and client. You may view traffic and also stick to it along with system flow.
It exhibits the flow structure of the TCP session and comprises a shark that’s just a tcpdump console variant (tcpdump can only be a package analyzer that runs onto a control line).
The only difficulty with Wireshark is the fact it has experienced Remote safety Exploitation.
8. Retina Network Security Scanner
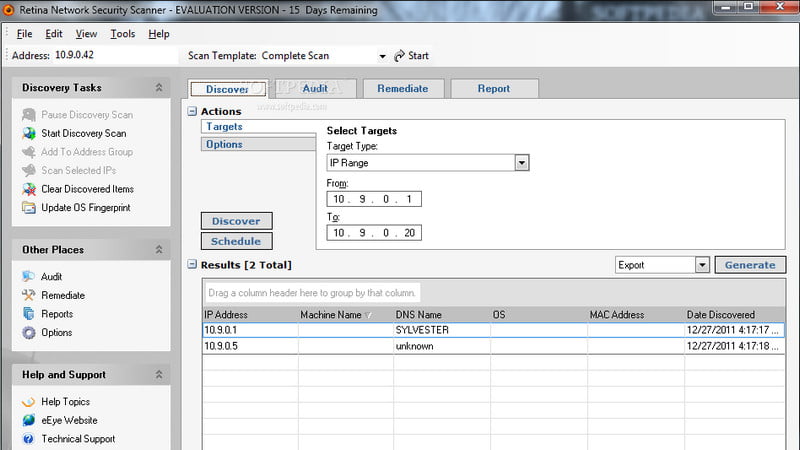
Over and above believe in’s Retina Network Security Scanner can be just really actually a vulnerability scanner and also a solution which likewise supplies security spots for Microsoft, Adobe, along with Firefox software.
It’s a standalone system vulnerability scanner system that affirms hazard appraisal centred on optimum network operation, operating programs, and software.
It’s an entirely free tool that demands a Windows host that supplies security stains to 256 IPs. This program implements scans following the qualifications furnished by an individual and allows a consumer to pick the sort of file shipping.
9. Metasploit Framework
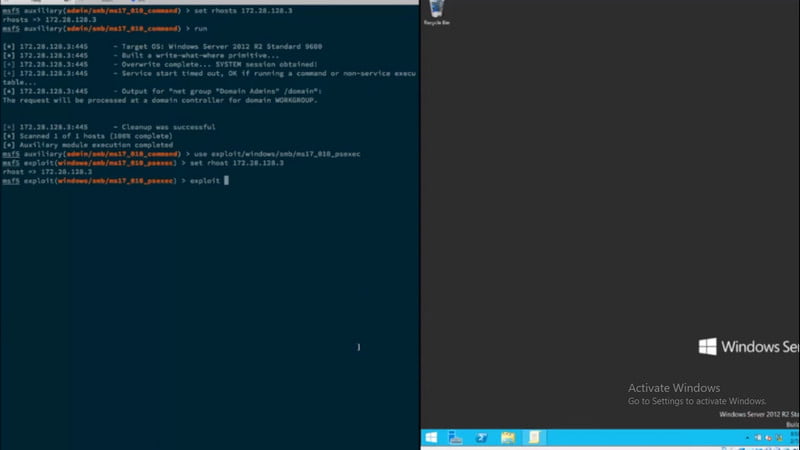
This application has been chiefly a Penetration Testing tool; nevertheless, it is like a community Scanning instrument that finds network use.
It had been an increasingly open-source application, but in ’09 it was obtained by Rapid7 and introduced like an industrial tool. An open-minded and completely free variant can be with confined stability features called a local community Edition.
The progress variant of Metasploit can obtain as Communicate Edition and the full-featured variant as best Version.
Metasploit Framework comprises Java-based GUI Whereas Local Neighborhood Edition, say, and best Edition contains internet-based GUI.
10. PRTG Network Monitor

PRTG community check will permit you to know more about the bandwidth that your apparatus and software are now employing to recognize the very foundation of bottlenecks. The remedy isn’t hard to utilize and is suited to practically any size.
Monitors system potential and utilization predicated in a routine like SNMP and supplied an online interface. Possesses include such as protection that is comprehensive, an adaptive alarm platform, and in-depth system observation.
PRTG community observing you can be just really a robust method that may test your whole infrastructure. These devices, apparatus, site visitors, and software on your IT infrastructure might track from the PRTG community observation.
It offers all of the functionalities, and there’s not any demand for plugins that are additional. With the assistance of both individually-configured PRTG detectors and SQL inquiries, you also can track certain data sets from the databases. It may offer in-depth figures for just about every single application on your system.
FAQ: Frequently Asked Questions
These are some of the frequently asked questions related to the Advanced IP Scanner with complete information.
Is Advanced IP Scanner legit?
Is it safe to use the tool? Yes, Advanced IP Scanner complies with Microsoft’s strictest security standards, ensuring that it runs smoothly in Windows.
How do I scan with an Advanced IP Scanner?
Here are the steps you need to follow in order to scan with an Advanced IP Scanner.
1.Open the Advanced IP Scan software by clicking on the following link:
2.To view what networks your computer is connected to, click the “IP” button:
3.Double-check the network address range you’re scanning:
4.To begin scanning the specified network, click the “Scan” button.
Does Advanced IP Scanner work on Mac?
Although Advanced IP Scanner is not available for Mac, there are a number of alternatives that provide similar functionality and work on macOS. Nmap, which is both free and open source, is the finest Mac option.
Wrapping Up
Inside the following piece, we’ve examined the very used and most popular system scanning applications. There can be far more aside from them.
You may select the most effective ideal for your own system depending on your networking behaviour to overcome system problems. Give a read to all of them.
Related Articles:
5 Ways on PS4 Games Remote Play In PC, TV, Phone
How to Fix Entry Point Not Found In Windows
How to Download Whole Playlist From YouTube
10 Intro Maker To Create YouTube Intro
How To Hibernate Windows 10 (Ultimate Guide)
How To Change Administrator Name In Windows 10
How To Record Screen And Audio on Mac QuickTime
15 Ways To Customize Laptop Like A Custom Laptops
This is Limit For Sending Emails For Gmail Mail Merge
How To Add Powerpoint To iMovie – Step By Step Guide
Find How Much Traffic Website Gets
How To Share Screen On Skype – Step By Step
How To Change Color of Start Menu In Windows 10
10 Valuable Ways To Get Rid From Credit Card Debt